GitHub Copilot cloud agent gets enterprise guardrails
GitHub turned Copilot cloud agent into a branch-first repo worker, then added signed commits plus org-wide runner and firewall controls that stricter teams actually need.

GitHub did not just give Copilot cloud agent more to do. It removed several of the reasons enterprise admins kept saying no.
GitHub's April 1 and April 3 Copilot cloud agent updates matter for a very unromantic reason: they remove the sort of objections that usually kill an enterprise pilot before the first branch appears.
In three days, GitHub turned Copilot cloud agent from a PR-opening helper into a branch-first repo worker, then added signed commits, organization-level runner controls, and organization-level firewall settings. I think that bundle is the real story. Plenty of agent launches promise autonomy. Fewer bother with the compliance goblins.
Copilot cloud agent can now work before the PR ritual begins
The April 1 changelog entry is where the product stops acting like it can only communicate through a pull request. GitHub says Copilot cloud agent can now work on a branch without opening the PR first, letting users review the diff, keep iterating, and create the pull request later. If you want the PR immediately, you can still ask for it.
That sounds modest. It is not. A PR-first workflow is fine for tidy chores. It is lousy for the messy middle, when you want the agent to inspect the repo, sketch an approach, make edits, and show its work before the review queue becomes a spectator sport.
GitHub also added implementation plans before code and deep research sessions for broad repo questions. The GitHub Docs overview says that on GitHub.com, Copilot can research a repository, create a plan, make code changes on a branch, and let you iterate before the PR.
That is the useful part of agent behavior. Not swagger. Prep work. Agents are good at reading twenty files and coming back with a diff. They are basically interns who never ask where the coffee is.
There is still a boundary. GitHub's docs say this richer research-plan-iterate flow is available on GitHub.com entry points such as the Agents tab and Copilot Chat there. Integrations such as Azure Boards, Jira, Linear, Slack, and Teams still create a pull request directly. So the PR-only model is gone in GitHub's main flow, not everywhere at once.
This also fits the broader repo-native pattern we have been tracking in GitHub Squad's repo-native multi-agent work and the AI coding agent orchestration bottleneck. Better agent work usually depends on better control surfaces, not louder claims.

Signed commits make Copilot cloud agent usable in stricter repos
Branch-first work is nice, but enterprises rarely stop at nice. They stop at branch protection.
The April 3 signed-commits update matters because GitHub says Copilot cloud agent now signs every commit it makes, with those commits showing as Verified. GitHub also says the agent can now work in repositories where the Require signed commits rule is enabled. Before that, the rule could block the agent entirely.
This sounds tiny until you meet the people who own the rulesets. In stricter repos, an agent that cannot satisfy signed-commit requirements is not a coding assistant. It is a guest in the lobby.
Branch-first iteration only matters if the branch can live under the same protections human contributors already follow. GitHub fixed that fast. I would not pretend this is some glorious age of autonomous development. It is something better: a plain governance blocker removed.
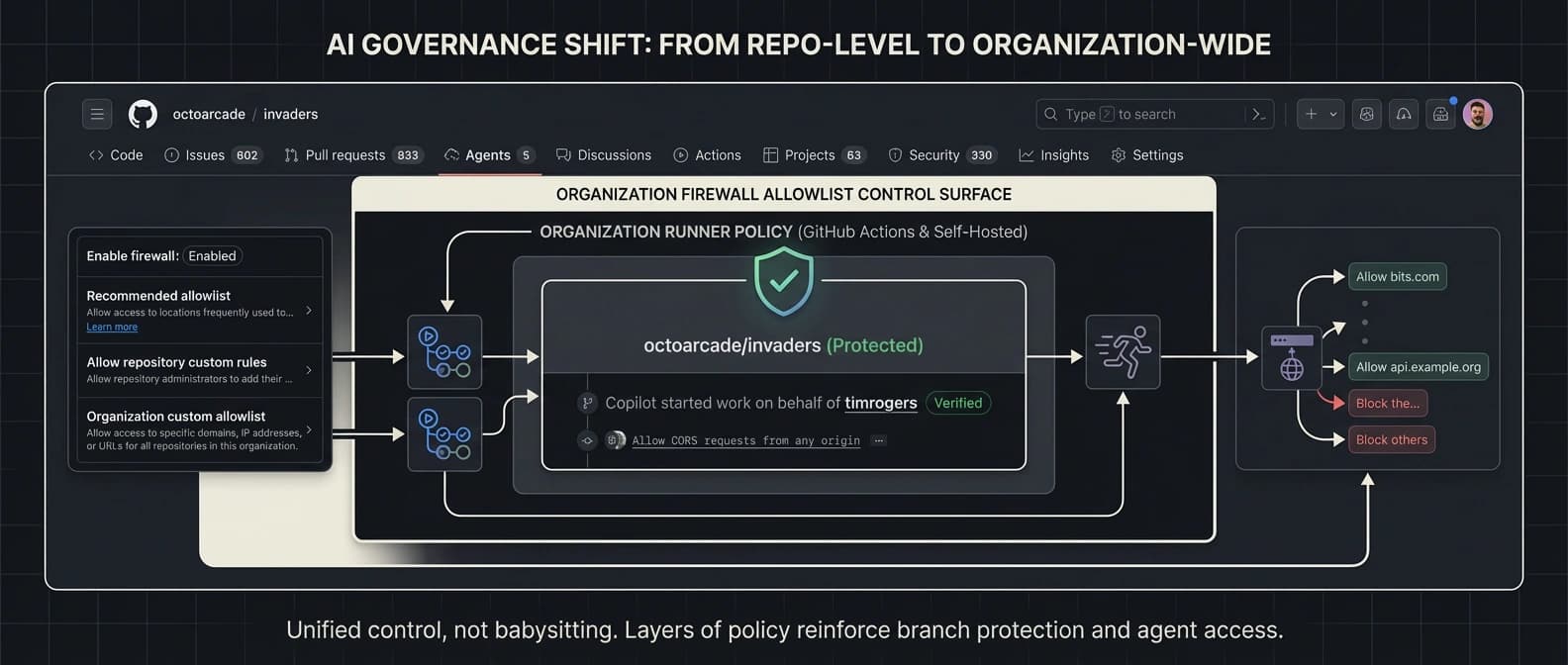
Runner controls and firewall settings give admins a real control lane
The same GitHub Docs overview says each Copilot cloud agent task runs inside its own ephemeral development environment powered by GitHub Actions. That is where platform teams start asking awkward questions. Which runner? Which network? Who can override the defaults?
GitHub answered part of that on April 3 with organization runner controls. Before this, runner choice lived at the repository level through copilot-setup-steps.yml, which made standardization annoying. Now organization admins can set a default runner across repositories and lock it so repositories cannot override it. That gives teams a cleaner way to steer Copilot cloud agent toward GitHub-hosted, large-runner, or self-hosted infrastructure.
The firewall update sits beside it. GitHub says Copilot cloud agent includes a built-in firewall to control internet access and reduce prompt-injection and data-exfiltration risk. The April 3 firewall update moves those controls up to the organization level. Admins can now control the firewall across repositories, manage the recommended allowlist, add organization-wide custom allowlist entries, and decide whether repository admins may add their own entries.
This is the part that made me laugh, because it is so gloriously unglamorous. GitHub did not spend this release cluster pretending governance was somebody else's homework. It gave admins knobs, locks, and fences. In enterprise software, that is half the romance.
Copilot cloud agent now looks pilotable for enterprise teams
The access-management docs keep one important caveat in view. For GitHub Copilot Business and GitHub Copilot Enterprise, Copilot cloud agent is disabled by default and must be enabled by an administrator. Repositories can still be opted out.
Still, the adoption math changed. Before April 1, Copilot cloud agent looked like a clever demo trapped inside a PR-first box. Before April 3, stricter repos and orgs still had obvious reasons to say no. Now the product supports branch-first work on GitHub.com, research and planning before code, signed commits for protected repos, org-level runner defaults, and org-level firewall policy.
That does not solve every concern. Some integrations still stay direct-PR only. Business and Enterprise rollout still depends on admin approval. If your team is arguing about model-training boundaries, that is a different conversation, and we covered it in GitHub Copilot's data usage policy. More broadly, the coding-agent market is moving toward repo-scale, workflow-heavy control surfaces, whether from GitHub, Qwen3.6-Plus, or install-surface plays like OpenAI Codex plugins.
But this GitHub update cluster is unusually concrete. I do not think Copilot cloud agent suddenly became an autonomous software deity. Spare me. GitHub removed several of the operational blockers that made it annoying to pilot in serious repositories. That is product maturity. It also gives platform teams something rare in agent rollouts: a pilot they can explain to auditors without sounding like they got conned at a conference booth. And in enterprise tooling, maturity is what gets you past the lobby.
Source file
Public source trail
These links anchor the package to the underlying reporting trail. They are not a substitute for judgment, but they do show where the reporting starts.
Canonical changelog entry for the April 1 branch-first update, including research mode, implementation plans, and iteration before opening a pull request.
Defines the product surface, GitHub.com versus integration behavior, the GitHub Actions-powered environment, and the admin-gated availability details that matter for enterprise use.
Confirms that Copilot cloud agent now signs every commit and can operate in repositories that require signed commits.
Introduces organization-level default and locked runner policies for the Actions environment behind Copilot cloud agent.
Adds organization-wide firewall and allowlist controls for the agent's outbound access.
Documents the Business and Enterprise admin gate plus repository opt-out rules, which frame the adoption question for stricter orgs.

About the author
Maya Halberg
Maya writes across the AI field, from research claims and benchmark narratives to tools, products, institutional decisions, and market shifts. Her reporting stays focused on what changes once hype meets deployment, procurement, workflow reality, and human skepticism.
- 24
- Apr 11, 2026
- Stockholm · Remote
Archive signal
Reporting lens: Methodology over launch theater.. Signature: A result only matters after the setup becomes legible.
Article details
- Category
- AI Tools
- Last updated
- April 11, 2026
- Public sources
- 6 linked source notes
Byline

Writes across the AI field with an eye for what survives contact with real users, real budgets, and real operating constraints.