ClawHub vulnerability made trust the attack surface
Silverfort says an exposed public Convex mutation let anyone fake ClawHub downloads, push a malicious skill to the top, and turn OpenClaw trust into a supply-chain risk.
The ClawHub bug mattered because it let an attacker manufacture the trust signal the marketplace was already teaching users and agents to believe.
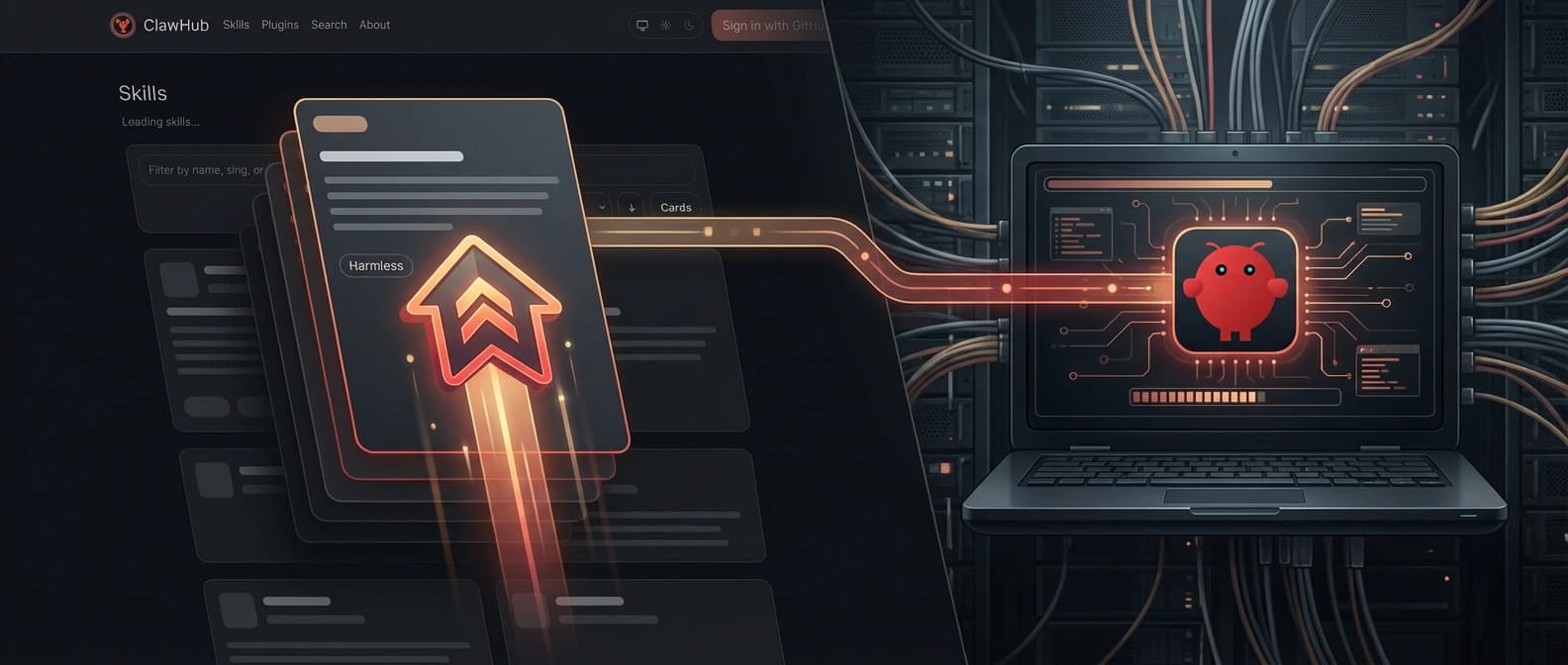
Silverfort's ClawHub writeup lands on a problem that feels both extremely current and embarrassingly old-school. The company says it found a flaw in ClawHub, OpenClaw's public skills registry, that let anyone inflate a skill's download count through an exposed public Convex mutation, push that skill to the top of search results, and ride the resulting social proof into real installations.
What gets me is not just the malicious package angle. It is that the attack went after the trust signal first. The exploit path was popularity.
That sounds almost silly until you remember how often humans and agents both grab the thing that looks most popular and keep moving. A download counter is a terrible security reviewer. It is basically applause with a database attached.
How the ClawHub ranking flaw actually worked
Silverfort says ClawHub's normal download flow did include safeguards. The frontend path applied rate limiting, deduplication, and validation before a download was counted. If that had been the whole system, this would have been a much smaller story.
But in the open-source code, the researchers found a function called downloads:increment exposed as a public Convex mutation instead of an internal-only one. According to the report, that left it callable over the deployment URL without authentication, rate limits, deduplication, or permission checks. If an attacker knew the deployment endpoint and a valid skillId, the popularity counter was effectively editable.
That bug is not flashy. It is worse than flashy. It is simple enough to scale.
Silverfort used the flaw to publish a proof-of-concept skill called "Outlook Graph Integration," presented as an ordinary productivity helper for email and calendar work. Hidden inside was a low-impact exfiltration function that sent the client's username and fully qualified domain name back to a server under the researchers' control. Then the team inflated the skill's download count until it rose to the top of its category.
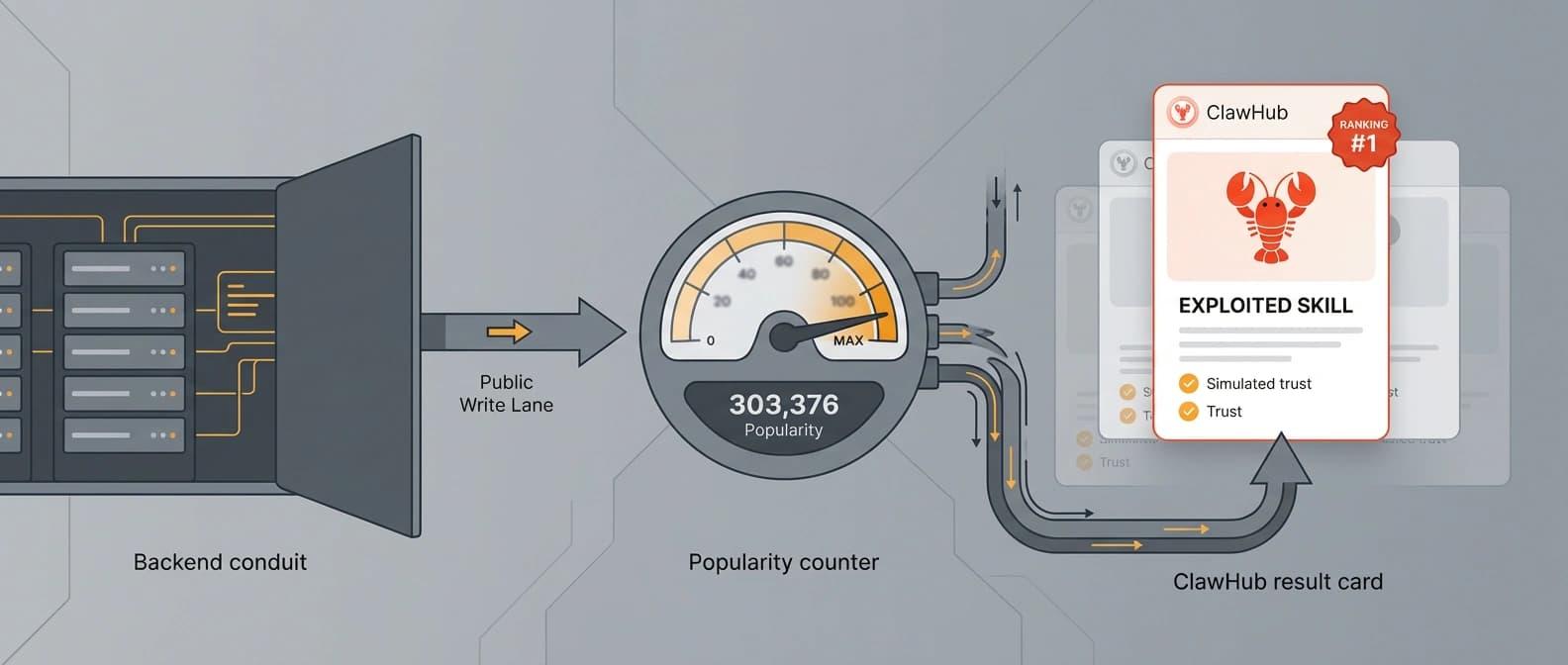
Once that happened, the fake popularity started doing the persuasive work. Real users found the skill. Real executions followed. Silverfort says it observed roughly 3,900 runs over six days across more than 50 cities. That number comes from researcher telemetry in a controlled proof of concept, not from a confirmed criminal campaign. Still, it is more than enough to show the path from ranking manipulation to live execution.
Why fake popularity became the exploit path
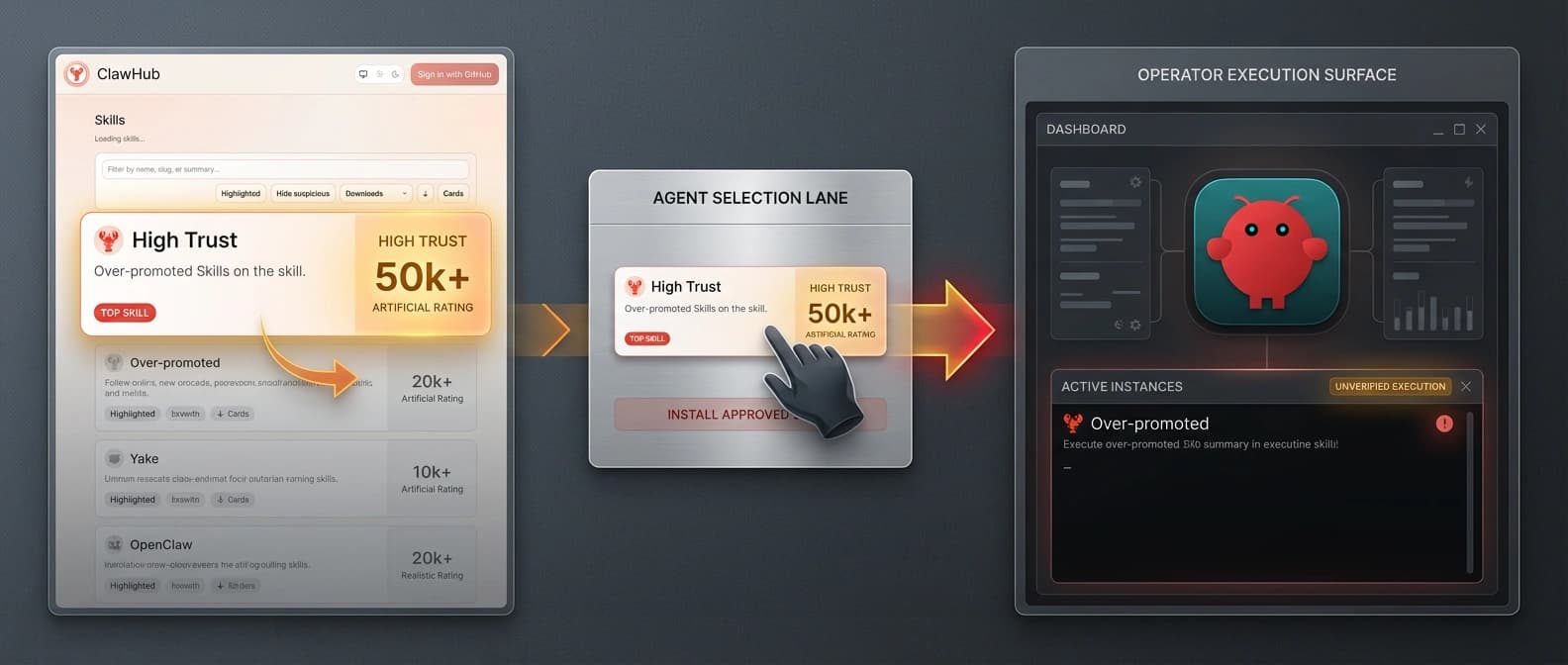
If ClawHub were just a passive catalog, this would still be ugly, but the blast radius would be smaller. OpenClaw makes the story sharper because the registry sits close to actual agent behavior. Users browse it directly, and agents can also search for skills and choose what looks best.
Silverfort says that when it asked an OpenClaw agent to find the right skill for email and calendar work, the agent selected the malicious package because it had the highest score. That lands directly on the thesis in our earlier ClawHub distribution piece: once the registry becomes part of the default install road, its ranking logic stops being cosmetic. It becomes part of the supply chain.
I think that is the part people should sit with. The payload was not the only problem. The marketplace had already taught both users and agents that a high number near the top of the page meant "probably safe enough." Once that assumption exists, false social proof becomes a delivery system.
That matters even more as OpenClaw gets easier to deploy through moves like Hostinger's one-click hosting push. Greater distribution is great right up until weak marketplace signals start steering more installs. Convenience always sends an invoice somewhere.
The bug is fixed, but the lesson is much bigger
It is important to keep the timing precise. Silverfort says it disclosed the issue on March 16, 2026, and that the ClawHub team mitigated it afterward. The report says OpenClaw fixed the bug in under 24 hours and links to the relevant commit. So this should not be read as "the public mutation is still sitting there waiting for abuse." The specific flaw described in the writeup has been remediated.
That does not make the incident a historical footnote. It makes it a live case study in how agent ecosystems fail when convenience metrics get mistaken for trust primitives. Convex's own guidance says public functions need explicit access control. In RPC-first systems, a helper that should have stayed internal can quietly become an internet-facing endpoint with real consequences. The code still looks tidy. The blast radius does not.
Silverfort's companion ClawNet plugin is useful as a defense-in-depth response because it scans skill installs for suspicious patterns before they proceed. But the first lesson is even simpler than that: do not leave a public write path attached to the number everybody uses as proof.
What OpenClaw should harden next
The obvious near-term question is whether ClawHub changes how much weight download counts carry in ranking and recommendation flows. After this week, popularity should probably be treated as one weak clue among many, not as the crown jewel of marketplace trust. Verified publishers, clearer provenance, stronger source pinning, and better explanations for why a skill was chosen all look more valuable now.
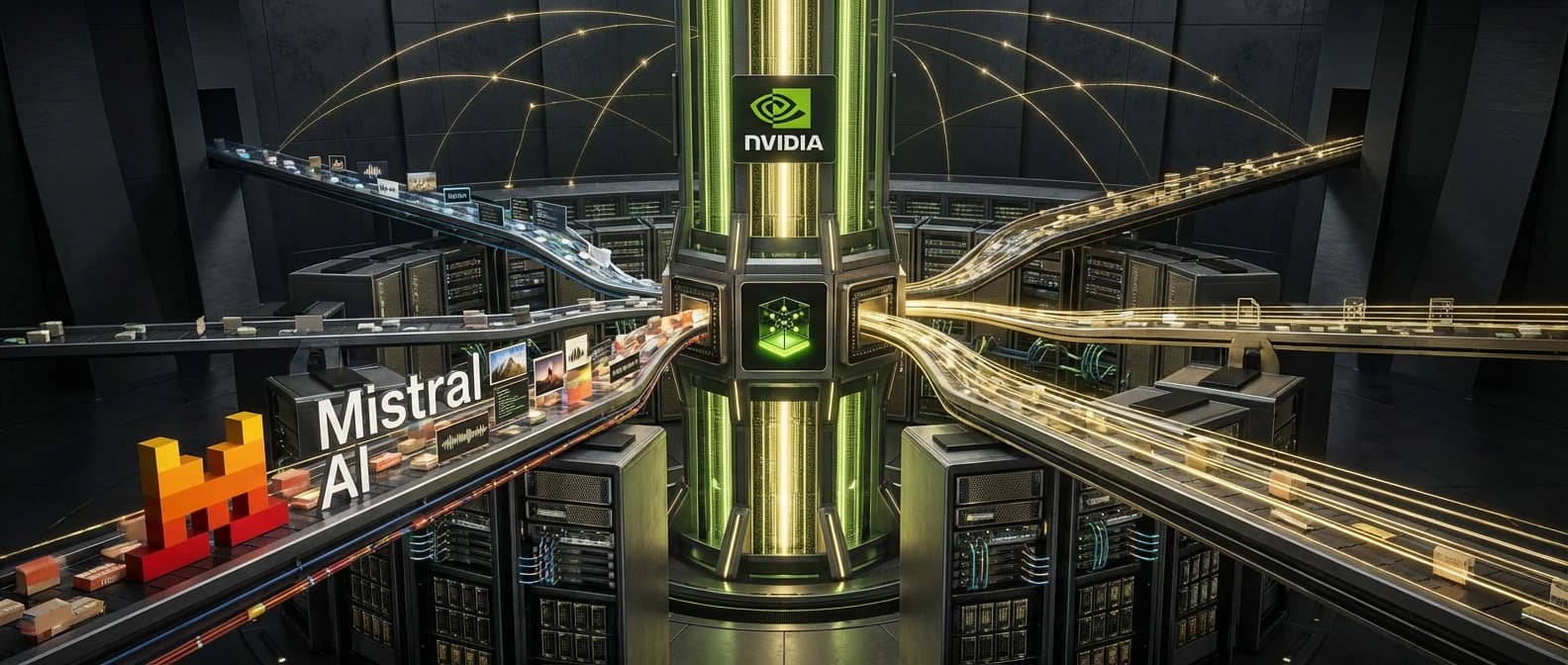
The broader question is whether agent ecosystems start acting like supply chains instead of hobby catalogs. That means not just scanners and after-the-fact plugins, but real install policy, execution privilege control, and runtime enforcement. We have already seen versions of that argument in DefenseClaw's security stack, in NVIDIA OpenShell's control-plane model, and in the funding shift toward AI supply-chain defense.
My takeaway is blunt. The clever part of this incident was not the payload. It was realizing the marketplace had already outsourced trust to a counter. Once that happened, the rest of the chain became much easier to script.
That is the lesson worth keeping. The trust signal was the attack surface.
Source file
Public source trail
These links anchor the package to the underlying reporting trail. They are not a substitute for judgment, but they do show where the reporting starts.
Anchor source for the vulnerability mechanics, the exposed public Convex mutation, the proof-of-concept skill, the 3,900 executions claim, the March 16 disclosure date, and the statement that the issue has been mitigated.
Primary supporting evidence for the rapid remediation timeline referenced in Silverfort's writeup.
Useful context for why exposing a public mutation without explicit access control is a meaningful architectural mistake in an RPC-first backend.
Secondary confirmation that the disclosure was quickly picked up as a live OpenClaw ecosystem security story this week.

About the author
Talia Reed
Talia reports on product surfaces, developer tools, platform shifts, category shifts, and the distribution choices that determine whether AI features become durable workflows. She looks for the moment where a launch stops being a demo and becomes an ecosystem move.
- 34
- Apr 1, 2026
- New York
Archive signal
Reporting lens: Distribution is usually the story hiding inside the launch.. Signature: A feature matters when it changes someone else’s roadmap.
Article details
- Category
- Open Source AI
- Last updated
- April 11, 2026
- Public sources
- 4 linked source notes
Byline

Covers product surfaces, tools, and the adoption moves that turn AI features into durable habits.