DefenseClaw shows OpenClaw has entered its security era
Cisco's DefenseClaw arrives just after NVIDIA's NemoClaw and a run of real OpenClaw attacks, turning agent security from a side note into the market forming around the platform.
Security markets usually appear the moment the cool demo acquires a pager.
I think OpenClaw has reached the moment every successful platform eventually meets: the part where security stops being a side note and starts becoming its own business.
Cisco’s DefenseClaw announcement matters to me less as a shiny launch and more as a market signal. It says OpenClaw is now big enough, exposed enough, and operational enough that people are building a real hardening stack around it. That is what happens when the cool demo acquires a pager. Suddenly everybody wants to know where the exits are and who has the keys.
The backdrop is not abstract agent anxiety. It is a series of very concrete warnings that changed the tone around OpenClaw.
OpenClaw now has a real attacker-shaped problem
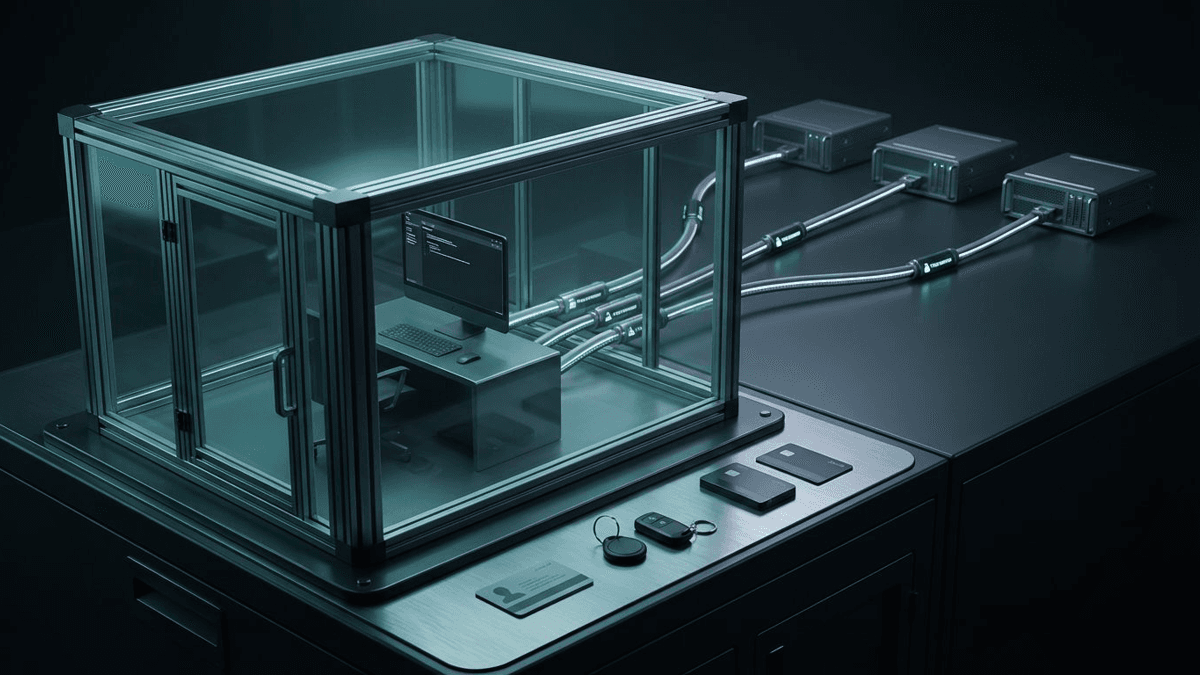
In a research release distributed by PR Newswire, Oasis Security described a chain where a malicious website could reach the local OpenClaw gateway over WebSocket, brute-force the password because localhost traffic lacked rate limiting, register itself as trusted, and then interact with the agent with full permissions. OpenClaw patched it quickly. The bigger lesson is simpler and less comforting: a browser tab had become part of the OpenClaw threat model.
Then OX Security reported an active phishing campaign aimed at OpenClaw developers through GitHub, using a fake openclaw.ai site and a crypto-wallet lure. Different attack. Same message. OpenClaw is no longer an obscure toy that only researchers bother poking. It is drawing ordinary criminal attention.
That distinction matters because platforms change once attackers treat them like a market. At that point, “we fixed the bug” is necessary but not sufficient. You need ongoing controls.
NemoClaw and OpenShell cover containment, not day-two operations
NVIDIA’s NemoClaw announcement and the NemoClaw repo tackled one layer of that problem. The repo is careful to say the stack is early preview and not production-ready yet, which I appreciate because launch honesty is rare and should probably be protected by law.
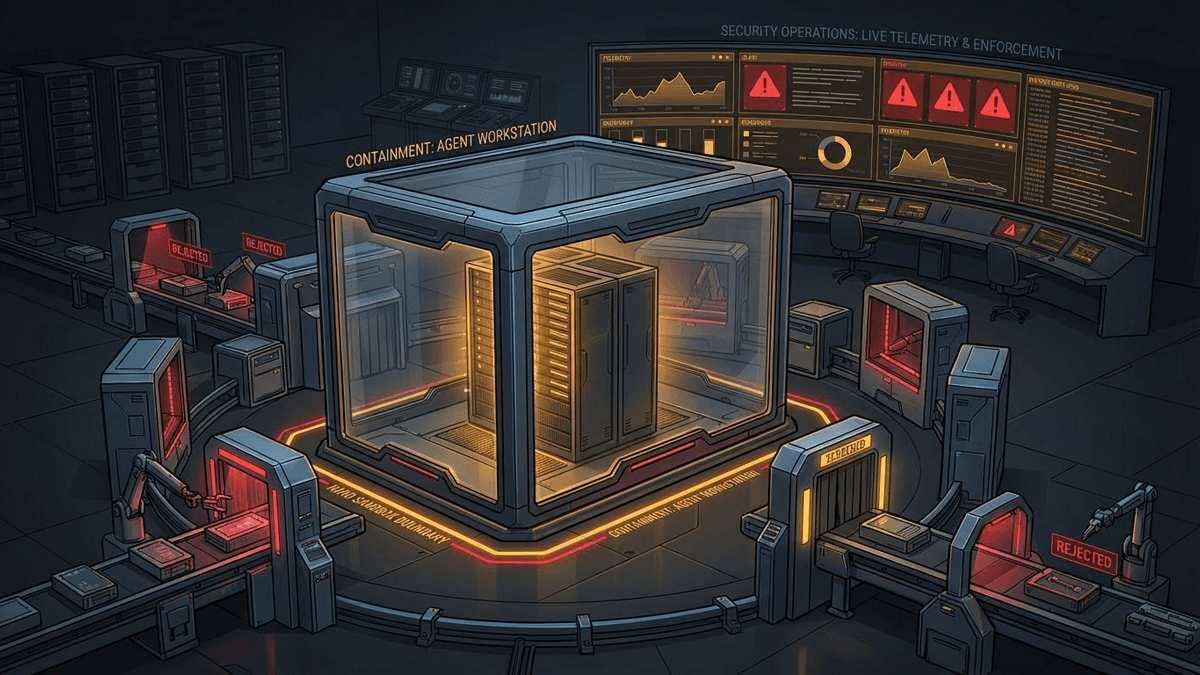
Even so, the architecture matters. NemoClaw wraps OpenClaw in OpenShell, applies filesystem and network policy from outside the agent, routes model access through controlled providers, and keeps raw credentials on the host. Deny-by-default egress is part of the pitch. So is the idea that the enforcement layer lives outside the model and can overrule it.
That is a real improvement. But containment is not the whole story. A sandbox can block a bad request. It cannot tell you whether a skill should have been trusted in the first place, whether generated code deserves admission, or whether the runtime has started acting strangely at 2 a.m. The walls matter. So do the guards.
DefenseClaw is trying to make policy enforcement operational
That is where Cisco positions DefenseClaw. According to Cisco, it sits on top of OpenShell and adds admission scanning, runtime inspection, and live enforcement that can revoke permissions, quarantine files, and cut network access without requiring a restart.
Cisco says the stack inspects skills, tools, plugins, and generated code before they enter the environment. It also watches runtime behavior instead of pretending Tuesday’s clean bill of health automatically holds on Thursday. That part is important. Supply-chain safety is not a vaccination you take once and forget.

The tell, for me, is the enforcement claim. Plenty of security products can describe risk in immaculate dashboards. The harder question is who gets to change the agent’s real behavior when policy trips. Cisco’s answer is that DefenseClaw can do that quickly through the OpenShell layer, while piping telemetry into Splunk from the start. If that works, DefenseClaw is less a scanner and more an operating layer.
My read on OpenClaw’s security era
Put the pieces together and the pattern is pretty clear. Threat researchers changed the baseline by showing OpenClaw could be attacked through ordinary web and phishing paths. NVIDIA answered with containment and external policy boundaries. Cisco is trying to add the next layer up: admission control, runtime monitoring, enforcement, and visibility somebody can actually own.
That is what a security era looks like. Not one magical product. A stack.
None of this proves DefenseClaw itself wins. Cisco’s announcement is still an announcement, and NemoClaw is still early preview. Usability, trust, and operator tolerance for extra friction will decide a lot. But the direction is unmistakable now. The interesting OpenClaw question is no longer just “what can this agent do?” It is “what can it do under policy, with logs, when connected to real systems?”
That is a much more mature question. Also a much more commercial one. The earlier OpenShell control-plane shift made that security boundary easier to imagine. DefenseClaw is the part that tries to make it operational. Security is not orbiting OpenClaw anymore. It is becoming one of the platform’s main ecosystems.
Source file
Public source trail
These links anchor the package to the underlying reporting trail. They are not a substitute for judgment, but they do show where the reporting starts.
Cisco's announcement defines DefenseClaw's role as the governance and observability layer on top of OpenShell.
Establishes the timing and positioning of NemoClaw and OpenShell as the new infrastructure layer beneath OpenClaw.
Adds implementation details such as early-preview status, policy behavior, sandbox lifecycle, and credential handling.
Details a browser-to-localhost OpenClaw vulnerability chain and the patch timing.
Documents a GitHub-based phishing campaign using a fake OpenClaw site and wallet-draining lure.

About the author
Lena Ortiz
Lena tracks the economics and mechanics behind AI systems, from serving architecture and open-weight deployment to developer tooling, platform shifts, product decisions, and the operational tradeoffs that shape what teams actually run. Her reporting is aimed at builders and operators deciding what to trust, adopt, and maintain.
- 24
- Apr 10, 2026
- Berlin
Archive signal
Reporting lens: Operating leverage beats ideological posturing.. Signature: If the cost curve moves, the product strategy moves with it.
Article details
- Category
- Open Source AI
- Last updated
- April 11, 2026
- Public sources
- 5 linked source notes
Byline

Covers the economics, tooling, and operating realities that shape how AI gets built, shipped, and run.